Risk Insider: Kevin Kalinich
Lights Out! Can Insurance Help?
In “Lights Out: A Cyberattack, A Nation Unprepared, Surviving the Aftermath,” author Ted Koppel suggests that a catastrophic cyber attack on America’s power grid is likely and that we’re unprepared.
Let’s examine his assertions from a risk management perspective.
• Power Grid Attack Likely?
Clients tell us that they are hacked more frequently than is reported. A Dec. 21, 2015 article, “Biggest U.S. Electric Company Battles Off Steady Cyberattacks,” reported that Duke Energy’s computer systems that manage dams, nuclear power plants and other types of generating plants are under constant attack. A reported cyber attack last month caused one-half of Western Ukraine to lose power.
• U.S. Unprepared?
Opinions differ on whether we have seen improved prevention, mitigation, response and resiliency since the Northeast power outage of 2003. Mr. Koppel described a bureaucracy that is moving slowly and with poor focus against a dynamic threat.
For example, the National Protection and Programs Directorate at the Department of Homeland Security, responsible for coordinating risk reduction to critical American infrastructure, is divided in two separate and distinct parts –- one physical and one cyber-related.
We are, however, seeing certain governmental actions and changes. The Cybersecurity Information Sharing Act of 2015, signed into law December 2015, provides immunity from liability to participating organizations that share certain cyber-threat information with the federal government and vice versa.
Federal and state agencies such as the Federal Energy Regulatory Commission may consider increased fines for grid failures that have ranged from $50,000 to $350,000. By way of example, Florida Power and Light Company was fined $25 million in 2009 for a February 2008 blackout.
However, most reported cases of cyber damage and regulatory action to date relate to protection of personally identifiable information, such as the Federal Communications Commission’s $25 million fine against AT&T and $100 million fine against Lifelock.
• Catastrophic?
According to search engine Shodan, the U.S. has more than 57,000 industrial controls systems connected to the internet. But how do we quantify potential losses? Information on how companies and the government respond to hacks is often protected and sometimes classified, which can defeat transparency.
A 2015 Lloyd’s of London/University of Cambridge report, “Business Blackout,” sets forth the insurance implications of a cyber attack on the U.S. power grid. The report estimated a hypothetical worst case scenario of $243 billion to $1,024 trillion in direct and indirect losses, with between $21.398 billion and $71.109 billion in estimated insurance industry losses.
Currently there are not enough stand-alone cyber limits to pay for such losses.
Many property and general liability insurers are inconsistent and/or hesitant to cover cyber exposures likely because there’s insufficient actuarial data. Since we don’t have sufficient actuarial data for cyber exposures, we should borrow from other complex modeling situations like typhoons, earthquakes and hurricanes — relatively rare events that could have catastrophic impacts.
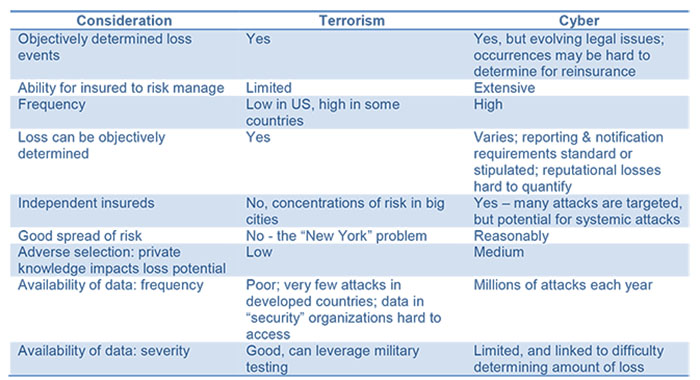
We’ve come to the conclusion that we need to break down the silos between the insurance company property/GL groups and cyber groups, and develop a combined all-risk policy that combines the actuarial data of property losses with cyber experts to identify and quantify frequency and severity. To analogize, a similar approach is used to build terrorism insurance programs, with mixed success (see graphic).
By combining an objective risk management context based on data analytics, we can learn from natural weather incidents and terrorism threats to develop robust public-private partnerships to help improve our preparedness and reduce losses stemming from a cyber attack.