Make Sure Your Data Recovery Firm Is Acting in Your Best Interests; A Smart Insurer Can Help
A recent piece by Pro Publica on the shenanigans of some data recovery firms should have gotten risk managers wondering whether the data recovery firms they use are on the up and up.
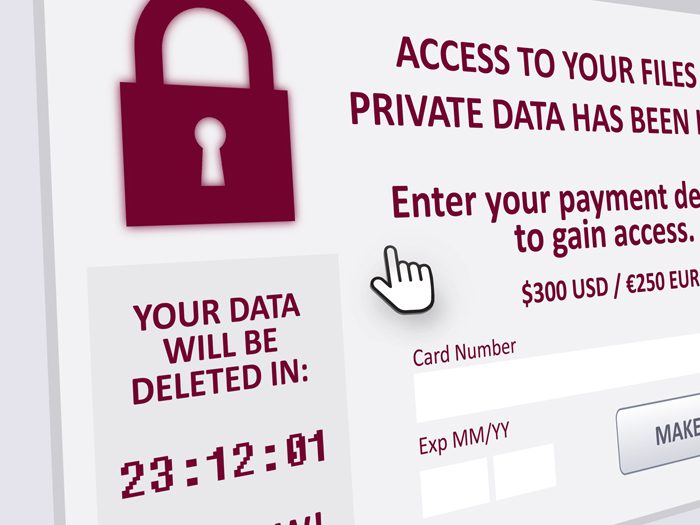
The piece detailed how some data recovery firms are selling themselves as forensic data companies, but when it comes to dealing with cyber thieves and ransomware demands, they’re just paying the ransom and not telling the client.
It’s a shady business practice and one that cyber specialists in the commercial insurance space decry.
“If you’re hiring them for a service, I don’t think it should be a secret in terms of what exactly is happening,” said Jeremy Gittler, practice leader and head of cyber claims Americas for AXA XL.
“Certainly if they are going to pay the ransom that is something that the victim should be aware of,” he added. “Because the decision that the victim has to make is ‘do you want to pay the ransom or not?’ ”
Insurers Work to Find the Right Firms
Commercial insurers that write stand-alone cyber coverage, Beazley being one, will have a stable of data recovery firms that they have spent quite a bit of time vetting to make sure they are capable of delivering on their promises and that function ethically.
Brett Anderson, a manager for Beazley Breach Response Services, said his company uses “under 10 firms that are comfortable enough to play in the sandbox of dealing with extortions.”
“There are plenty of firms that we work with that do not do that sort of thing,” Anderson added.
Anderson said before Beazley brings a data recovery firm into the fold, that firm will undergo extensive vetting.
“It often takes between six to eighteen months before we will introduce a new type of vendor to our policy holders,” said Anderson.
Working with a commercial insurance carrier that has a trustworthy team of forensics firms is becoming more advisable than ever because the pace of ransomware attacks is ever increasing.
According to a report released by Beazley on May 23, ransomware attacks increased by 105% between the first quarter of 2018 and the first quarter of 2019. There was a corresponding 93% increase in the average ransom demanded or paid, from $116,324 to $224,871, the UK-based insurer reported.
Beazley said that while attacks using ransomware as a service (Raas) platforms remain commonplace, tending to hit small businesses, more sophisticated variants are being deployed through phishing emails and tricking users into activating banking Trojans.
Originally designed to steal banking credentials from users of online banking websites, according to Beazley, recent variants of banking Trojans such as Emotet and Trickbot have been used by criminals to harvest all kinds of account details, the company said in a press release.
Being Upfront on Paying Ransom
The Pro Publica piece seemed to tilt in the direction of viewing the payment of a ransomware demand as some type of failure, but both Gittler and Anderson said their firms pay ransoms frequently.
The economic decision the insured has to make in many cases is weighing the cost of extensive business interruption against the cost of the ransom.
“Most of the time we do pay the ransom,” said Gittler. “What it comes down to is your business is down, you need to get up and running.
“The first thing we look at is A) can we decrypt the ransom ourselves and usually we can’t,” he said. “B) is do you have the proper backups? I would say that if everything you have that is on lockdown is on proper backups than you can likely say ‘fine, we don’t need it.’ But we still need to investigate what information, if any, was exfiltrated. And are the threat actors still in the system?”
He said cyber thieves these days are so sophisticated they will end up locking up the back-up systems as well.
Having said that, Gittler added there is some “honor among thieves.”
“In almost every instance where you do pay the ransom you do wind up getting the decryption key,” he said.
What’s changed in recent years, according to Beazley’s Anderson, is that these days the ransom amount is not known until you reach out to the attacker who has frozen your system.
“Before 2017, a lot of the ransoms were being displayed in the notes, but these days they are no longer being displayed,” he said.
Anderson said keeping up with patching and using multi-factor authentication for external access to networks are two key security measures that firms should be employing.
Gittler said the narrative outlined in the Pro Public piece, with a “data recovery” firm paying the ransom and not telling the client, would not happen with a company insured by AXA XL.
“The whole scenario in the article would never really happen with us, because besides us working with the firms, you have an attorney involved. The whole point of the attorney is to make sure everything is being taken care of pursuant to law,” Gittler said.
“You want to make sure there are no lawsuits. You want to make sure the regulators are satisfied. You are never going to be dealing with a sketchy firm that is doing underhanded things.” &












