Cybercriminals Abandon Encryption for Data Extortion, Raising Stakes for Risk Managers

Cybercriminals have fundamentally rewritten their playbook, abandoning encryption-based ransomware for simpler but more damaging data-theft tactics, according to Resilience’s 2025 Cyber Risk Report.
Extortion-only incidents climbed from 49% of cases in the first half of 2025 to 65% in the second half, signaling that the primary risk to enterprises is no longer going offline but rather enduring a sustained financial, regulatory and reputational crisis that can unfold over years, the report said.
“Cyber risk is constantly changing. As cybercriminals shift their tactics, a new reality is setting in: the real risk is about more than a security incident’s immediate disruption, it’s about the long-tail aftershocks that follow,” said Vishaal Hariprasad, CEO and co-founder of Resilience.
A New Criminal Playbook Takes Hold
The shift away from encryption reflects both mounting law enforcement pressure on ransomware operators and a straightforward cost-benefit calculation: stealing data is operationally simpler, harder to defend against and cannot be remediated through backups alone. Rather than deploying complex encryption infrastructure, threat actors now steal data, threaten to publish it and collect payment — a lean model that has proven highly effective, the report said.
Compounding the challenge, AI-generated phishing campaigns achieved a 54% success rate in 2025, compared to just 12% for traditional phishing, Resilience said. AI phishing campaigns are 4.5 times more effective than traditional phishing, according to research from Harvard University cited in the report.
That surge in 2025 translated directly into higher-severity claims, with phishing-related losses exceeding $1.6 million per claim and accounting for 50% of losses where the point of failure was known, up from 22% in 2024. Critically, these attacks increasingly led to ransomware and extortion demands rather than lower-stakes outcomes, the report said.
On the identity front, infostealers — malware that harvests credentials and session tokens — captured 2 billion credentials in the first half of 2025 alone, according to Resilience. This transformed credential theft into the primary precursor for major enterprise breaches. These tools enable attackers to hijack sessions and bypass certain multi-factor authentication implementations, the report said.
Meanwhile, wrongful data collection claim notices more than doubled year over year, driven by litigation targeting website tracking practices, including the use of tracking pixels and the sharing of visitor information with third parties, the report noted.
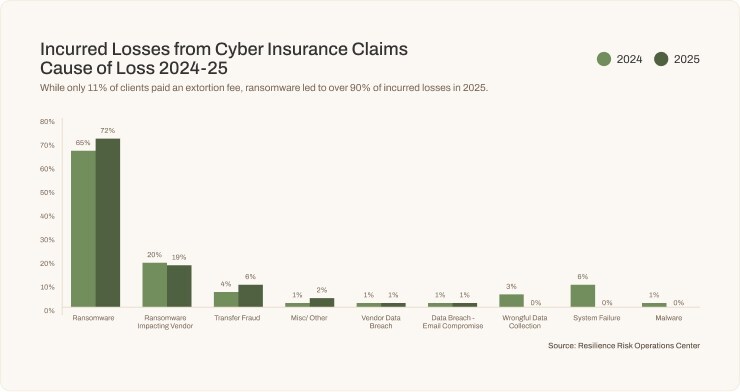
Concentrated Losses Reshape the Insurance Landscape
The tactical pivot toward data extortion reshuffled which organizations absorbed the most damage. Manufacturing, health care and retail together accounted for 68% of all portfolio losses — each sector vulnerable in distinctly different ways, according to Resilience.
Manufacturing held the top position for total losses, though average severity fell approximately 29% from 2024, likely reflecting improved backup and incident response capabilities across the sector. Nonetheless, just-in-time supply chains and aging operational technology keep manufacturers uniquely exposed, as extended downtime cascades quickly to customers and downstream partners, the report said.
Health care remained the highest-severity sector on a per-incident basis, driven by the long-term criminal value of electronic health records and the life-critical pressure that forces hospitals to weigh patient safety against security best practices. A re-extortion case in the sector affected more than 5 million patient records through a single vendor compromise — illustrating how third-party exposure can dramatically amplify health care’s risk profile, Resilience said.
Retail was 2025’s most dramatic story, jumping from near-zero material losses in 2024 to a $2.6 million average severity in 2025, the report said. The escalation was driven almost entirely by the Scattered Spider group’s May 2025 campaign targeting major UK retailers — including Marks & Spencer, Co-op and Harrods — before spreading to U.S. brands. The Marks & Spencer attack alone took 45 days to restore online ordering functionality, with weekly losses exceeding £40 million ($54 million).
Building Resilience for a Multi-Year Risk Environment
With claim timelines now routinely extending two to three years as litigation, forensic accounting and regulatory proceedings run parallel tracks, insurance coverage and incident response strategies built on historical averages are insufficient for today’s environment, according to Resilience. Organizations across all sectors need limits that reflect current severity levels, with particular attention to transfer fraud, extortion and contingent business interruption protections.
On the security investment side, the data points toward three high-priority areas: defenses against AI-powered phishing, identity protection to counter credential compromise, and data loss prevention aimed specifically at the growing share of extortion attacks that bypass encryption entirely.
Incident response frameworks also need a fundamental update, the report said. Technical recovery must now be paired with immediate legal mobilization — lawsuits can materialize within days of an incident, sometimes before organizations have a clear picture of what occurred.
Obtain the full report here. &