The Profession
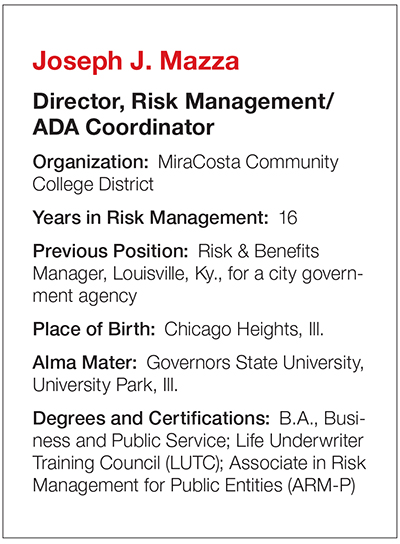
Joseph J. Mazza
During my senior year in high school, [I worked] as a custodian every night and full time on Saturdays for $1 an hour. I had the run of the school. It turned into a summer job at $1.25 an hour after senior year!
R&I: How did you come to work in risk management?
Having started as an insurance agent in life, health, and then property and casualty in 1975 at John Hancock … I wanted to explore company exposures beyond the insurance field. … I worked for a multiline commercial insurance agency and then a national retailer insurance program for franchisees with Ace Hardware for 20-some odd years. I enrolled in the Associate in Risk Management (ARM) program in 1997 and 1998, and was hired the next year by DaimlerChrysler.
R&I: What’s been the biggest change in the risk management and insurance industry since you’ve been in it?
For risk management, the biggest change has been heightened visibility and a better understanding of what it is and how it can drastically impact the bottom line of any entity. For insurance, it’s the speed and communication between underwriters and the producer with the advent of technology. Keep in mind I started in the “write back” days of waiting and waiting for snail mail to arrive.
R&I: What emerging commercial risk most concerns you?
As everyone currently considers data breaches a primary concern, I will go with that one too, and have implemented an insurance policy for my district accordingly. … The main focus here would be protection of data for employee records, student records, financial aid records and other important data we have in our computer systems. If we had a breach, it would be devastating.
R&I: How would you rate the insurance industry’s response to cyber risk?
Excellent so far with corresponding rate increases coming now that more purchasers are coming on board. Those insured losses need to be paid by someone. I think the frequency of cyber risk is increasing, and that frequency can cause a big severity problem.
R&I: Who is your mentor and why?
Most recently, Edwin Hall, a former regional manager with DaimlerChrysler, who had a great way of understanding and managing people. For my insurance career, it was Al Klipstein, who was an agent when I was with John Hancock. His personality matched mine and I learned so much about the business from him as he was highly successful and a great source of information.
R&I: What have you accomplished that you are proudest of?
Building relationships with colleagues in and out of my entity is the main one. I have been able to implement important driver authorization programs for district drivers. Serving as the San Diego RIMS chapter president for two years in 2012 and 2013 and being awarded the Risk Professional of the Year designation for my chapter in 2008 are very special to me too. I have found that my sense of humor has really helped break the ice and build rapport and it makes my life and career more enjoyable.
R&I: What insurance carrier do you have the highest opinion of?
I like both ACE and AIG as they are both equally high-quality carriers, with AIG returning to an important spot in the marketplace since the financial crisis.
R&I: Are you optimistic about the U.S. economy or pessimistic and why?
Being a born optimist, I am hopeful that the free market system really gets back to the growth days we saw several decades ago.
R&I: What is the best restaurant you’ve ever eaten at?
Antoine’s Restaurant in New Orleans. My wife and I once had a meal there in the early ’90s that ended with the server pouring a liquor-based sauce for dessert on the white tablecloth and lighting it! No one got burned and it was just a wonderful dinner. I’m not sure they still do that, but it was special.
R&I: What is the most unusual or interesting place you have ever visited?
Cumberland Falls State Park near Corbin, Ky., has a moonbow, the only one in the Western Hemisphere. You know what a rainbow is — here there is an actual “moonbow” at night!
R&I: What is the riskiest activity you ever engaged in?
Forcing myself to speak publicly, for someone with the fear of doing so, is very risky. It was dreadful the first few times. After that, I learned to find a few people to focus on in the front row and to make eye contact with them. If there’s a large group I will stand at the front door and introduce myself as the speaker or presenter. Now you aren’t speaking to a room of strangers; you’re not going in cold. It’s a technique that a lot of people can use.
R&I: What about this work do you find the most fulfilling or rewarding?
Since we are an educational institution, what is most fulfilling to me is serving faculty and students in a support role and making our district a great place to learn and succeed.
R&I: What do your friends and family think you do?
They know I was the “insurance guy” for years and then when risk management came along they did not understand it … . At one time, I told them I was in the witness protection program and earned a good living doing that — just kidding!