Is Ransomware Protection Even Plausible? Here’s What the Experts Say

Had there been no pandemic, 2021 could well have been the year of ransomware.
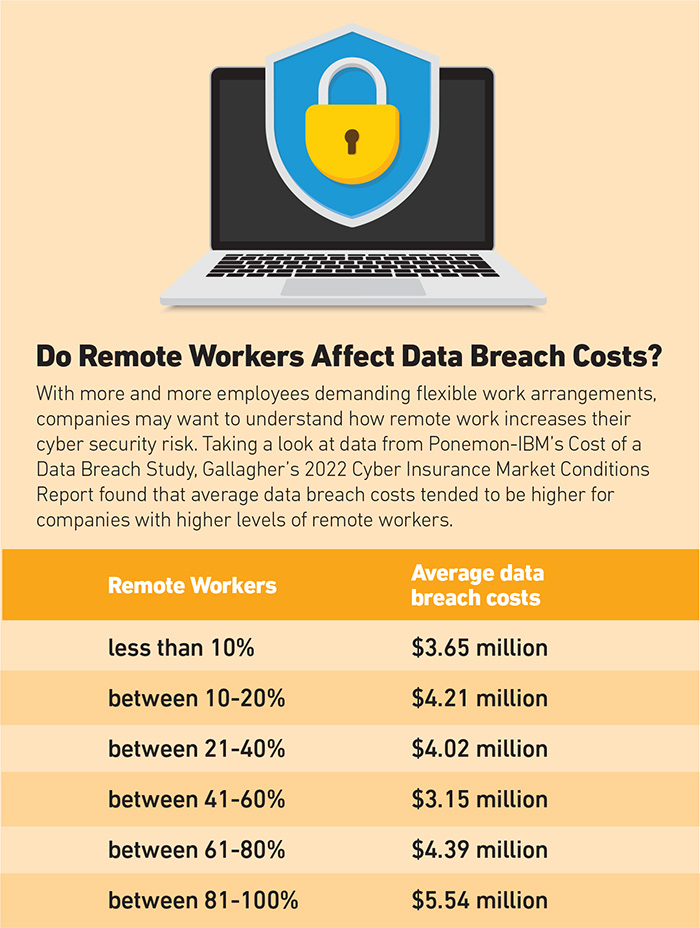
Companies spent $590 million on ransomware payments in the first six months of 2021 — a number that has already exceeded the $416 million paid in all of 2020, per Gallagher’s “2022 Cyber Insurance Market Conditions Report.”
As of November 2021, there was a 62% increase in the frequency of ransomware attacks, Allianz Global Corporate & Specialty (AGCS) noted in their “Ransomware trends: Risks and Resilience” report.
In some ways, ransomware is a tale as old as time. There have always been criminals out there looking to steal and extort. Instead of Bonnie and Clyde pulling up to a bank and whipping out a fire arm, we now have anonymous hackers, clicking away and launching attacks from the comfort of their homes.
“Pirates have moved from the ancient sea lanes to stage coaches and trains to brick and mortar banks. Now they’ve moved into the digital environment, and they’re after your data.” —Bob Lloyd, executive vice president, Brown & Brown Insurance
“Pirates have moved from the ancient sea lanes to stagecoaches and trains to brick-and-mortar banks. Now they’ve moved into the digital environment, and they’re after your data,” said Bob Lloyd, executive vice president for Brown & Brown Insurance.
Whether bank robbery or ransomware attack, criminals are motivated by one thing: cold hard cash. “Someone once asked Slick Willie Sutton, the bank robber, ‘Why did you rob banks?’ And his answer was simple: ‘I robbed banks because that’s where the money is,’ ” Lloyd continued. “It’s the same thing with ransomware.”
As the threat of ransomware is ever-evolving and unyielding, carriers are beginning to restrict coverage for the costly attacks. Risk managers are shifting their focus to cyber security strategies and employee training in an attempt to remain attractive to insurers.
The Anatomy of a Ransomware Attack

Bob Lloyd, executive vice president, Brown & Brown Insurance
The first ransomware attack arrived in 1989 when Harvard-educated biologist Joseph L. Popp mailed 20,000 floppy disks to attendees of World Health Organization’s AIDS conference.
The disks purportedly contained a questionnaire for determining a person’s likelihood of contracting HIV. But users found that the disks actually blocked them from accessing their files and demanded that they mail $189 to a post office box in Panama to regain access.
Since then, cyber criminals have been using ransomware to lock up company networks and demand payments.
More and more companies now keep backups of their data, but attackers are resorting to increasingly unscrupulous tactics, including threatening to expose company and client data if the ransom is not paid. Companies of every size and sector are vulnerable to this kind of attack.
“They are actually contacting key clients of the initial victim, telling that client of the initial victim that they are going to expose their data if the primary target doesn’t pay,” said John Farley, managing director, Gallagher’s Cyber Liability Practice.
“They’re taking data hostage, but they’re also threatening to expose very sensitive data if they’re not paid.”
Beyond the threat of data exposure, executives may be tempted to pay ransoms because of their disruptive effect on company operations. The average downtime from a ransomware attack was 23 days and business interruption costs totaled $1.85 million in 2021, Gallagher reported.
“They’re sort of damned if they do, damned if they don’t,” Lloyd said.
“If they pay it, they may be in trouble from an insurance coverage standpoint or from a regulatory standpoint. If they don’t pay it, they risk substantial and maybe permanent damage to their company.”
Caught in this tough situation, many companies opt to pay the ransom. Thirty-three percent of businesses hit with a ransomware attack in 2019 decided to pay out, according to reporting from Forbes.
But paying a ransom doesn’t guarantee you’ll get your data back. Of the organizations that paid ransoms 22% never got their data back and nine percent were attacked again, per Forbes’ report.
Get Ready for Rate Increases
Carriers are starting to shy away from ransomware risks in response to the increasing frequency and severity of attacks. Cyber, a line that historically had ample capacity, has now been tightening limits, imposing sub limits and raising rates.
“We’re seeing carriers pivot in a way where they’re trying to limit their own exposure to the ransomware epidemic,” Farley said.
“We’re no longer in the soft market that we have seen in years previously,” added Sally Li, VP, head of cyber underwriting, AmTrust.
“The hardening rates are driven by the amount of activity the carriers have been seeing. There’s been an increase in ransomware activity, but also just an increased awareness of cybersecurity risks in general.”
 Some carriers are imposing sub limits specific to ransomware claims: “If you have a $10 million cyber policy, there is a chance that your carrier will impose mandatory sub limits when a ransomware attack occurs,” Farley said. “So, you may only get 50% of the limit if the claim involves a ransomware attack.”
Some carriers are imposing sub limits specific to ransomware claims: “If you have a $10 million cyber policy, there is a chance that your carrier will impose mandatory sub limits when a ransomware attack occurs,” Farley said. “So, you may only get 50% of the limit if the claim involves a ransomware attack.”
Exclusions are also coming into play. Cyber underwriters are taking a hard look at zero-day vulnerabilities, a type of software flaw that developers are unaware of or unable to fix. “Some carriers are adding exclusions specific to that known vulnerability,” Sam Levine, senior vice president, CAC Specialty, said.
Others are increasing rates for cyber insurance policies.
“There’s some pretty significant tailwinds inflating price points for our clients,” said Robert Rosenzweig, cyber practice leader, Risk Strategies.
“The rate trends throughout 2021 were like a rocket ship. We probably started Q1 of last year in the low 20% increase range, and by the end of the year, we were up to that 89% mark.”
“We saw that those price increases moved more into the 80%, 90%, 100% range on a year over year basis in the second half of 2021,” added Christian Hoffman, global cyber leader, Aon.
A Hard or Correcting Market?

Gwenn Cujdik, manager, North America cyber incident response team, AXA XL.
Some are hesitant to say that cyber insurance markets are hardening, however.
“It’s not so much a fear to pull away from writing cyber insurance, but it’s writing it in a more intelligent way so that everybody benefits in the long run,” said Gwenn Cujdik, manager, North America cyber incident response team, AXA XL.
“We’ve learned a lot, based off of the claim activity from the last few years, and all of that’s been built into an underwriting process,” added Tracie Grella, AIG’s global head of cyber.
In many cases, insurers aren’t pulling back coverage entirely. Underwriters are just asking additional questions about the steps organizations are taking to prevent ransomware attacks. Some are even requiring supplemental applications focused on ransomware risks.
“Insureds really need to be looking at the security questionnaires and ransomware questionnaires that the underwriters are putting out and making sure that their practices are in line with all of the questions that are being asked,” Levine said.
Carriers hope this approach will help create a market where ransomware risk is manageable.
“Insurance and risk mitigation — which is security — work together. Transfer reduces the impact of loss events. Mitigation reduces the likelihood of the impact occurring for loss events,” said Rich Seiersen, CSO, Resilience Cyber Insurance Solutions.
“It’s not so much a fear to pull away from writing cyber insurance, but it’s writing it in a more intelligent way so that everybody benefits in the long run.” — Gwenn Cujdik, manager, North America cyber incident response team, AXA XL.
To that end, carriers are implementing risk management and attack response services. Maria Long, lead for FrameWRX Allied World’s cyber risk management platform, heads up one such platform.
She emphasized that carriers need to help insureds understand what cyber risk management tools they need to have on hand in order to make their risks insurable.
Risk Management Tools to Keep You Above the Fray

John Farley, managing director, cyber liability practice, Gallagher
In order to make themselves more attractive to carriers, companies need to implement robust cyber security measures.
Using VPNs, multifactor authentication (MFAs) and other security tools will be key to ensuring a smooth renewal.
Of these tools, MFAs are especially critical. MFAs can prevent attackers from getting into a company’s system by requiring users to enter two pieces of identity verification to enter a system.
“Multifactor authentication is one of the key cybersecurity controls in preventing ransomware attacks, and underwriters are demanding it,” Farley said. “Without MFA, there’s a very good chance that your cyber policy will not be renewed.”
VPNs are another useful tool. VPNs hide users IP addresses and encrypt their traffic and data, making it harder for attackers to target them with ransomware.
Additionally, employers will need to address the human factor of a cyber-attack. Oftentimes, attackers exploit workers in order to gain access to a system through phishing hacks.
“Human error is a huge element when it comes to ransomware attacks, specifically phishing emails,” Long said.
Addressing this risk will involve companies implementing mandatory cyber security tests and training for workers. Companies should send out simulated phishing emails to see which of their employees may be vulnerable to clicking on a malicious link. Additional training can help support those employees and reduce risks.
“Without MFA, there’s a very good chance that your cyber policy will not be renewed.” —John Farley, managing director, Gallagher’s Cyber Liability Practice.
“Get into a cycle of training and awareness annually — or more often than annually — that brings fresh perspective to employees,” Lloyd said. “Don’t think of it as you can do this one time and check the box for underwriting your cyber liability policy, and then forget about it. You have to keep it fresh and you have to keep it meaningful.”
“They should be interactive. You should be engaging the employees in a way that isn’t just staring at a computer or sending emails,” Cujdik added.
In the event an attack occurs, underwriters will want to see that a company has backed up their data and can get back up and running in a timely manner. Regularly testing backups and your firm’s ability to restore those backups in a matter of hours can help underwriters feel more comfortable taking on ransomware risks.
“If the downtime is less there is a lower probability that the insured is going to need to pay that ransom demand to regain access to their network and their data,” Rosenzweig said.
All these requirements may seem like a lot for businesses, but they’re necessary to remain abreast of risk in an ever-evolving tech world.
“The frustrating thing for a lot of our clients is the goal posts are constantly moving. It’s not because insurers are trying to pull the rug out from underneath them, but we’re in a very fluid environment where the threat landscape is evolving and technology continues to improve and there’s vulnerabilities that present themselves,” Rosenzweig said.
Cyber insurance policyholders may experience challenging renewals in the years to come, but those in the industry believe there is light at the end of the tunnel.
“The optimist in me says that the underwriting community has worked harder than ever to properly underwrite the risk, and clients have generally responded to help try and manage it,” Farley said. &
 Courtney DuChene was recognized as the winner in the “Insurance & Risk Technology Journalist of the Year” category for the Willis Towers Watson 2023 Journalist of the Year award. Her reporting in the above article contributed to her win.
Courtney DuChene was recognized as the winner in the “Insurance & Risk Technology Journalist of the Year” category for the Willis Towers Watson 2023 Journalist of the Year award. Her reporting in the above article contributed to her win.