Risk Report: Entertainment
On With the Show

Recent hacks on the likes of Sony, HBO and Netflix highlight the vulnerability entertainment companies have to cyber attack. The threat can take many forms, from the destruction or early release of stolen content to the sabotage of broadcast, production or streaming feeds.
“Cyber attacks are becoming the biggest emerging threat for entertainment companies, bringing risk to reputations, bottom lines and the product itself,” said Brian Taliaferro, entertainment and hospitality specialist, JLT Specialty USA.
For most entertainment firms, intellectual property (IP) is the crown jewel that must be protected at all costs, though risk profiles vary by sub-sector. Maintaining an uninterrupted service may be the biggest single concern for live broadcasters and online streaming providers, for example.
In the case of Sony, North Korea was allegedly behind the leak of stolen private information in 2014 in response to a film casting leader Kim Jong Un in what it considered an unfavorable light.
This year, Netflix and HBO both faced pre-broadcast leaks of popular TV series, and Netflix last year also had its systems interrupted by a hack.
Online video game platforms are also ripe for attack, with Steam admitting that 77,000 of its gamer accounts are hacked every month.
The list goes on and will only get more extensive over time.
Regardless of the platform, any cyber attack that prevents companies from producing or distributing content as planned can have huge financial implications, particularly when it comes to major releases and marquee content, which can make or break a financial year.
“People and culture are the biggest challenges but also the keys to success.” — David Legassick, head of life science, technology and cyber, CNA Hardy
The bottom line, said David Legassick, head of life science, technology and cyber, CNA Hardy, is that these firms have a combination of both assets and business models that are inherently open to attack.
“Vulnerabilities exist at every point in the supply chain because it’s all tech-dependent,” he said, adding that projects often run on public schedules, allowing criminals to time their attacks to maximize impact.
“The combination of IP, revenue and reputation risk make entertainment a hot sector for cyber criminals.”
Touch Point Vulnerabilities
Film, TV, literary and music projects invariably involve numerous collaborators and third-party vendors at every stage, from development to distribution. This creates multiple touchpoints through which hackers could gain access to materials or systems.
According to Kyle Bryant, regional cyber manager, Europe, for Chubb, there is nothing unique about the type of attack media companies suffer — usually non-targeted ransomware attacks with a demand built in.
“However, once inside, the hackers often have a goldmine to exploit,” he said.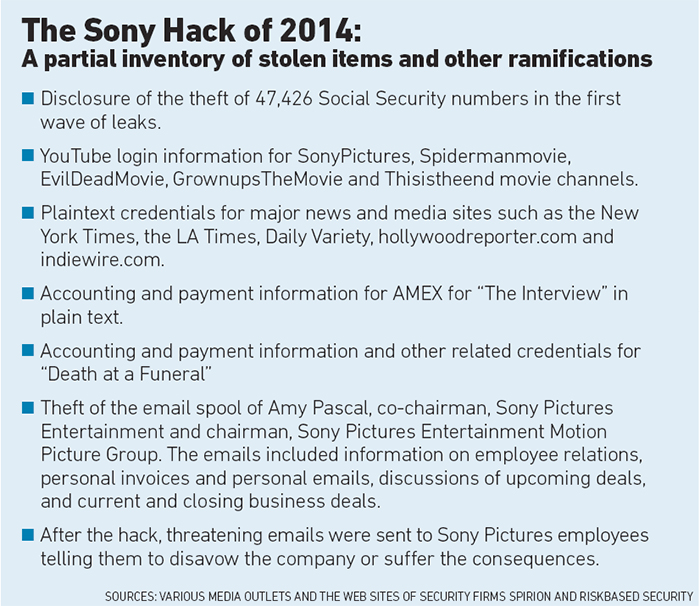
He added targeted attacks can be more damaging, however. Some sophisticated types of ransomware attack, for example, are tailored to detect certain file types to extract or destroy.
“NotPetya was designed to be non-recoverable. For a media company, it could be critical if intellectual property is destroyed.”
As entertainment companies have large consumer bases, they are also attractive targets for ideological attackers wishing to spread messages by hijacking websites and other media, he added.
They also have vast quantities of personal information on cast and crew, including celebrities, which may also have monetary value for hackers.
“It is essential to identify the most critical information assets and then put a value on them. After that, it is all about putting protection in place that matches the level of concern,” Bryant advised.
As with any cyber risk, humans are almost always the biggest point of vulnerability, so training staff to identify risks such as suspicious messages and phishing scams, as well as security and crisis response protocols, is essential. Sources also agree it is vital for entertainment companies to give responsibility for cyber security to a C-suite executive.
“People and culture are the biggest challenges but also the keys to success,” said Legassick.
“Managing the cyber threat is not a job that can just be left to the IT team. It must come from the top and pervade every aspect of how a company works.”
Joe DePaul, head of cyber, North America, Willis Towers Watson, suggested entertainment companies adopt a “holistic, integrated approach to cyber risk management,” which includes clearly defining processes and conducting background checks on the cyber security of any third party that touches the IP.
This includes establishing that the third parties understand the importance of the media they are handling and have appropriate physical and non-physical security at least equal to the IP owner in place. These requirements should also be written into contracts with vendors, he added.
“The touchpoints in creating content used to be much more open and collaborative, but following the events of the last few years, entertainment firms have rapidly introduced cyber and physical security to create a more secure environment,” said Ryan Griffin, cyber specialist, JLT Specialty USA.
“These companies are dealing with all the issues large data aggregators have dealt with for years. Some use secure third-party vendors, while others build their own infrastructure. Those who do business securely and avoid leaks can gain an advantage over their competitors.”
Quantification Elusive
If IP is leaked or destroyed, there is little that can be done to reverse the damage. Insurance can cushion the financial blow, though full recovery is very difficult to achieve in the entertainment space, as quantifying the financial impact is so speculative.
As Bill Boeck, insurance and claims counsel, Lockton, pointed out, there are only “a handful of underwriters in the world that would even consider writing this risk,” and sources agreed that even entertainment firms themselves struggle to put a monetary value on this type of exposure.
“The actual value of the IP taken isn’t generally going to be covered unless you have negotiated a bespoke policy,” said Boeck.
“If you’re in season five of a series with a track record and associated income stream, that is much easier, but putting a value on a new script, series or novel is difficult.”
Companies for whom live feeds or streaming are the primary source of revenue may find it easier to recoup losses. Determining the cost of a hack of that sort of service is a more easily quantifiable business interruption loss based on minutes, hours, ad dollars and subscription fees.
Brokers and insurers agree that while the cyber insurance market has not to date developed specific entertainment products, underwriters are open for negotiation when it comes to covering IP. The ball is therefore in the insured’s court to bring the most accurate projections to the table.
“Clients can get out of the insurance market what they bring to the equation. If you identify your concerns and what you want to get from insurance, the market will respond,” said Bryant.And according to Griffin, entertainment companies are working with their brokers to improve forecasts for the impact of interruptions and IP hacks and to proactively agree to terms with underwriters in advance.
However, Legassick noted that many entertainment firms still add cyber extensions to their standard property policies to cover non-physical damage business interruption, and many may not have the extent of coverage they need.
Crisis Response
Having a well-planned and practiced crisis response plan is critical to minimizing financial and reputational costs. This should involve the input of experienced, specialist third parties, as well as numerous internal departments.
“The more business operation leaders can get involved the better,” said Griffin.
Given the entertainment industry’s highly public nature, “it is critically important that the victim of a hack brings in a PR firm to communicate statements both outside and within the organization,” said Boeck, while DePaul added that given that most cyber attacks are not detected for 200-plus days, bringing in a forensic investigator to determine what happened is also essential.
Indeed, said Griffin, knowing who perpetrated the attack could help bring the event to a swifter and cheaper conclusion.
“Is it a nation state upset about the way it’s been portrayed or criminals after a quick buck? Understanding your enemy’s motivation is important in mitigating the damage.”
Some hackers, he noted, have in the past lived up to their word and released encryption keys to unlock stolen data if ransoms are paid. Inevitably, entertainment firms won’t always get so lucky.
Given the potentially catastrophic stakes, it is little surprise these firms are now waking up to the need for robust crisis plans and Fort Knox-level security for valuable projects going forward. &













