How the Medical Industry Can Close Coverage Gaps and Stem Huge Losses from Cyber Attacks
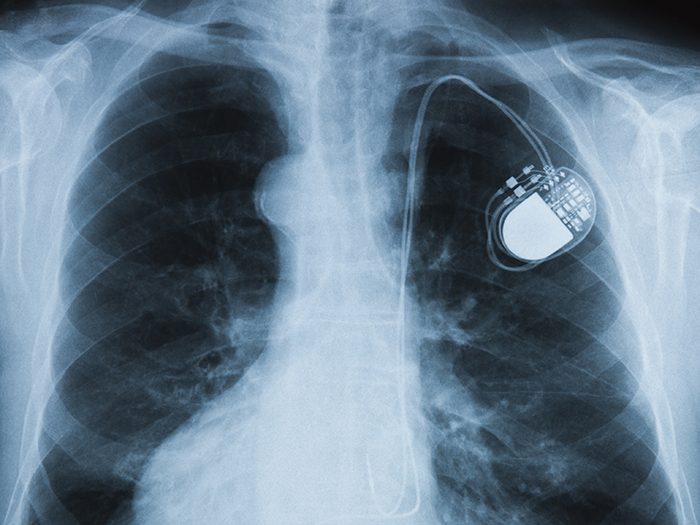
Connecting medical devices to network systems and the internet greatly enhances their functionality and effectiveness in patient care. But connected devices often provide windows of opportunity for cyber criminals looking for a vulnerability to exploit.
This is an area of increasing concern with the rise of telemedicine and a growing reliance on electronic medical devices throughout every facet of health care. Consider the devastating effects of 2017’s Not Petya attack. While a Ukrainian accounting company was the initial victim of the attack, any company “connected” to them through email or electronic connectivity was quickly infected.
Hundreds of health care organizations, particularly in the UK, were impacted or shut down. The inability to access electronic patient care systems because of a “cyber-weapon” has a direct impact on patient care and could lead to grave errors and adverse patient outcomes.
If a medical device is hacked, every party along the supply chain is at risk, from device and software manufacturers and sellers, to hospitals and individual health care providers. But coverage for those risks is not one size fits all, and significant coverage gaps may exist.
Where Are the Gaps?
Beecher Carlson recently published its Cyber Coverage Handbook for Medical Devices report, highlighting those potential gaps, and offering guidance on how companies can better connect the dots of their insurance programs to close those gaps and avoid unpleasant surprises.
“Understanding the interaction between Professional, product, property, cyber and other insurance policies and implementation of a coordinated insurance program for all conceivable cyber risks is critical to a leading strategy,” wrote the report’s authors.
What’s in the Report?
The report examines coverage concerns from three distinct angles: health care providers, medical device manufacturers including software, service or parts providers, and sellers of medical devices. Exposures and potential gaps can vary broadly for each.
Beecher Carlson’s handbook breaks down risks and coverage options for a half-dozen scenarios related to medical devices, including:
- Cyber-caused bodily harm to patients
- Medical device exploit causing business income loss
- Medical devices used as attack devices
- Cyber extortion threats
- Breach of patient confidentiality
- Recall
Where Else Can I Find Help?
On December 28, 2018, the U.S. Department of Health and Human Services released the “Health Industry Cybersecurity Practices (HICP): Managing Threats and Protecting Patients” publication, which provides voluntary cybersecurity practices designed to reduce security risks and improve security for health care organizations.
With respect to connected medical devices, the Cybersecurity Guidelines recommend that organizations consider these practices:
- Establish and maintain communication with medical device manufacturer’s product security teams.
- Patch devices after patches have been validated, distributed by the medical device manufacturer, and properly tested.
- Assess current security controls on networked medical devices
- Assess inventory traits such as IT components that may include the Media Access Control (MAC) address, Internet Protocol (IP) address, network segments, operating systems, applications, and other elements relevant to managing information security risks.
- Implement pre-procurement security requirements for vendors.
- Implement information security assurance practices, such as security risk assessments of new devices and validation of vendor practices on networks or facilities.
- Engage information security as a stakeholder in clinical procurements.
- Use a template for contract language with medical device manufacturers and others.
- Implement access controls for clinical and vendor support staff, including remote access, monitoring of vendor access, MFA, and minimum necessary or least privilege.
- Implement security operations practices for devices, including hardening, patching, monitoring, and threat detection capabilities.
- Develop and implement network security applications and practices for device networks. &










