Cyber Fraud
The Weakest Link

It’s not easy being responsible for fraud prevention at a major corporation. The methods of attack are multiplying, the tactics ever more sophisticated and Machiavellian. It’s hard to keep up with all the new monikers for these techniques, let alone ensure your organization is impenetrable.
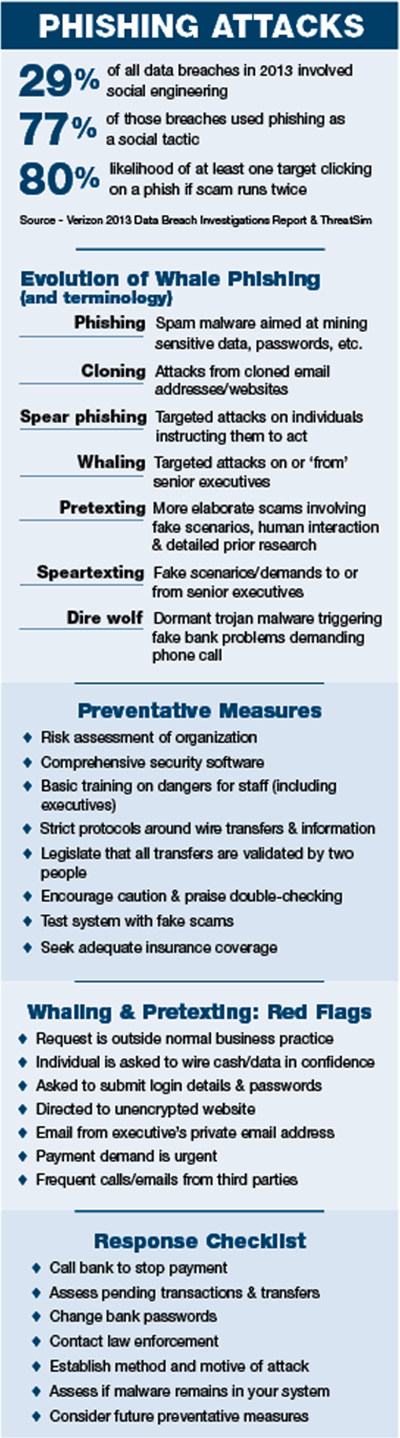
The infection of systems with malware through spam-like phishing attacks evolved some years back into “spear phishing” of specific individuals, using gathered personal information about them to make the attacks seem more believable. “Whale phishing” or “whaling” is spear phishing but for bigger fish — in other words, CEOs, CFOs and other senior executives with the power to authorize major money transfers or release sensitive data.
One recent scheme attacked the CEOs of 20,000 organizations and succeeded in implanting malware in the systems of 2,000 of them.
Most organizations have caught on to malware-based attacks, and have various layers of software protection in place to identify and block any suspicious activity. But wise to the fact that malware alone might not be good enough, fraudsters are increasingly using human interaction, simulating situations and impersonating individuals, organizations and authorities to get what they want.
IBM researchers have reportedly uncovered a new type of attack they are dubbing “dire wolf,” whereby malware from an attachment sits dormant within an organization’s network until it detects a user is navigating to a bank website. It then creates a fake pop-up frame telling the user the website is having problems and to call a number for help with their banking needs.
At the end of the phone is an English-speaking operator who asks for confidential login details — as soon as this information is given the fraudsters immediately access the user’s bank account and instruct a large wire transfer.
Scams involving thorough background research to inform the invention of false scenarios, websites and companies are known in some quarters as “pretexting.”
Richard Thomas, principal of Ernst & Young’s fraud investigation and dispute services practice refers to the tailoring of these attacks to individual targets as “speartexting.” Don’t be surprised if that term is the next to enter the lexicon.
One of the most prevalent “speartexting” scams (see — it’s catching on) is for an individual in the finance department of a company to be sent an email purportedly from the CEO, CFO or senior executive informing them the company is involved in a highly confidential acquisition and the individual will shortly receive communication from a major law firm sending wire transfer instructions — and due to the sensitive nature of the deal, this must be kept secret.
Thanks to the mining of information from personal emails, private servers and publicly available sources, the hackers are able to convincingly portray the executive’s tone and may, for example, know he or she is on first name terms with the finance person — who is likely flattered the CEO has chosen them for this task. The target then receives a call or email from a fake lawyer, providing wire instructions and reiterating the importance of confidentiality. You know the rest.
“These fraudsters prey on human nature — the desire to help clients, solve problems right away and frankly to protect their own jobs. That’s a very effective play,” said Greg Bangs, chief underwriting officer of global crime at XL Catlin.
Industry Impact
The scale of this kind of crime, and its cost to corporate America is unfathomable — literally. There is no reliable data on the monetary value of losses associated with this new wave of sophisticated spearing scams but it undoubtedly runs into billions of dollars. According to sources, individual losses so far have ranged from tens of thousands to, staggeringly, tens of millions.
It’s safe to assume the gangs perpetrating these crimes — believed primarily to operate in Eastern Europe, Russia, China and other parts of Asia — are now extremely wealthy.
“It’s incredibly lucrative for the fraudsters,” said EY’s Thomas. “The more clients I speak to about this issue, the more I hear of it being successful. And it’s costing companies more than just the loss — there is then the cost associated with investigating the issue and increasing controls to prevent it happening again. Billions of dollars are being spent annually on protecting companies in the U.S.”
The cost of these so-called “socially engineered” schemes is particularly difficult to gauge, not only because the practice is relatively new but also because so many instances go unreported.
“These fraudsters prey on human nature — the desire to help clients, solve problems right away and frankly to protect their own jobs.” — Greg Bangs, chief underwriting officer of global crime, XL Catlin
“Many organizations don’t want their customers thinking there is a failure in their systems or a weakness in their controls so they brush it under the carpet,” said XL Catlin’s Bangs.
“We strongly recommend all attacks be reported to the police. The only way we are going to stop these people is by providing law enforcement with enough information about ongoing scams to help them prevent them before they get worse.”
“Companies need to decide whether they want to stop the fraud and keep it internal or try to control the fraud, get law enforcement involved and hope they’ll be able to one day catch the criminals and possibly recover their money or other people’s lost money,” said Chris Giovino, director of forensic investigation, crime and cyber evaluation risk quantification at Aon Global Risk Consulting, adding, “If you’ve already sent a wire transfer within the last 24 hours the bank has a strong chance of freezing the account and having the money returned before it washes out to another account.”
The latest scams have primarily been aimed at large organizations due to their attractive bounties and array of executives to target. However, anyone can become a victim and the attackers are moving down the food chain.
“Perhaps not ‘mom and pop shops,’ but smaller private companies and nonprofits will be as vulnerable to this as larger organizations going forward,” said Bangs.
Michael Peters, himself a certified hacker (one of the good ones), computer forensic examiner, and IT director for the Risk and Insurance Management Society (RIMS), believes Wi-Fi is the weak spot most likely to be exploited in the next generation of scams.
“The more our world advances towards wireless technology, the more people trust entering their private details over wireless connections. Cars and planes now offer wireless technology, which is going to open up a plethora of vulnerability for hackers to target,” he said.
This is bad news considering the chances of recouping money or catching the criminals in the wake of a successful scam are low, and most traditional insurance policies still don’t cover this kind of loss as they fall in the gap between conventional crime and cyber policies.
“We are not having a lot of success in recovery through crime policies when it comes to social engineering losses,” Giovino said. “It’s a very gray area, but I do know that brokers, on behalf of policyholders, are working with carriers to address this and some carriers are rewriting policies to be more inclusive and bring them up to date.”
Response and Prevention
EY’s Thomas said it is vital companies put response plans in place so they can react quickly if they fall victim to an attack.
“The first priority for businesses is to recover lost data or money — call the bank; stop the payment,” he said, noting that it is not uncommon for companies to get so caught up in establishing how they were duped that they neglect to take this fundamental step.
Companies should immediately change their banking passwords, obtain a list of pending transactions and recent wire transfers, and inform law enforcement, he added.
“You then need to understand what has happened — the goal of the perpetrator; whether there is an insider threat, either deliberately or inadvertently, from someone in the organization; and whether there are any ‘sleeper mechanisms’ within the network that could be deployed against you at a later date,” Thomas explained. This, of course, requires the expertise of internal or third party IT experts.
Next, companies need to establish how they can control their environment to ensure they don’t become victims again.
“Companies can fight back from a pre-loss position, as this is preventable,” said Giovino, placing the risk manager at the heart of the process.
“The risk manager is pivotal. Although this sounds like a security or finance problem, the risk manager is the person in the company who owns the problem because the loss is potentially insurable and restitution or recovery can only come from insurance.”
The first line of defense is the best and latest software to filter out as much suspicious activity as possible. RIMS’ Peters is responsible for protecting not only his organization but the data of 11,000 member companies, and employs four layers — or “sentries” — of protection and redundancies, from anti-spam and anti-malware programs to desktop client protection.
But the biggest challenge with social engineering is that it preys more on human behavior than system flaws.
“You are only as strong as your weakest link, which is your end user,” admitted Peters. That’s why organizations must implement written protocols and procedures, backed up with staff training to instill awareness — as well giving staff the confidence to question their superiors if they smell a rat.
Indeed, Bangs added, that training must include senior executives too as they are primary targets.
 “The protocols in most companies are now adequate — it’s the training portion that can make a big difference,” said Giovino.
“The protocols in most companies are now adequate — it’s the training portion that can make a big difference,” said Giovino.
“If a company [mandates that] anyone initiating a wire transfer must have secondary approval, it must be inculcated into the mindset of everybody that this policy cannot be overridden — even by the CEO or president.”
“I do believe that with a combination of training and a hard look at technology and processes, companies can mitigate most of this risk,” added Thomas.
Once software, protocols and training have been implemented, the system should then be tested with fake scams to root out potential weaknesses.
The final defense against social engineering is insurance — although not everyone can access it yet.
“The insurance industry has not kept up with the exposure or developed response policies,” said Peters. And that, broadly speaking, is true — traditional commercial crime, funds transfer fraud or computer fraud policies are unlikely to provide cover because these crimes involve individuals or organizations being coerced to act of their own accord; the criminal does not actually steal the property themselves, nor do they use the target company’s computers to do it.
AXIS is one of only a handful of insurers to have already developed a social engineering fraud coverage endorsement as part of its commercial crime insurance product, addressing the risks organizations face when cyber criminals pose as senior executives to manipulate employees into transferring funds.
“Our decision was to be more proactive rather than reactive to this evolving need for coverage,” said Lisa Block, vice president and commercial crime product manager at AXIS. “Social engineering is a hot topic of discussion in the crime insurance sector right now. Instead of remaining silent on this issue as some carriers have, we decided to offer an affirmative statement of coverage for this specific type of loss.”
And it appears the tide is turning. “The insurance industry is very focused on this,” Thomas said. “Companies are concerned. As dialogue continues, we continue to see changes in the way companies address this risk through insurance and how insurers address this risk in their policies.”
“We feel that crimes of this nature that result in a financial loss for insureds should be legitimately covered going forward,” added Bangs, revealing that XL Catlin will also roll out a product extension later this year covering social engineering fraud, also known as fraudulent impersonation.
But carriers won’t issue coverage without carefully assessing an insured’s ability to protect itself.
Yet more reason to ensure the culture of caution and awareness seeps through every pore of every organization. The cyber criminals are, as ever, one step ahead of corporate America.
Only education, and a willingness by victim organizations to come forward when attacked, can erode their advantage.











