R&I Exclusive
The Science of Slips and Falls: Building a Better Floor-Safety Program

Slips and falls are the second greatest cause of accidental deaths each year, according to OSHA data, right behind motor vehicles.
Nearly 25 percent of reported claims stem from a slip, trip or fall, and many of them could have been prevented, which is why CNA chose to take a deep dive into the unique factors behind these all-too-frequent events.
“The American National Standards Institute provides guidance on hard surface flooring materials for slip resistance testing. CNA used tribometry as a baseline for determining the slipperiness of the floor,” said Shari Falkenburg, assistant VP, Risk Control, CNA. Tribometry is the measurement of friction on a surface, in this case measuring the traction between an individual’s feet and the floor.
In a new study entitled “Enhancing Floor Safety Through Slip Resistance Testing, Maintenance Protocols and Risk Awareness,” CNA Risk Control walkway specialists reviewed slip and fall liability claims from Jan. 1, 2010 to Dec. 31, 2016 to gain insight as to how and why these accidents occur.
The specialists then spent two years testing floors in commercial settings — from retail trade to construction — during pre- and post-cleaning, breaking the research into two main components: cleaning agents and floor material.
“Depending on the type of floor, selecting the wrong cleaning agent could impact the slipperiness of the floor,” said Steve Hernandez, senior VP, Risk Control, CNA. “In addition, selecting improper cleaning equipment and tools could also contribute to floor slipperiness. This information helped to better understand the root cause behind slip and fall claims.”
CNA’s findings are that floor type and the cleaners used on them play significant roles in a surface’s coefficient of friction — the presence of traction between an individual’s feet and a surface. Cleaners react with floor types differently, which in turn can create a number of workplace hazards.
Materials Matter
Cleaning agents used on floors were broken down into four categories: alkaline-based, acidic-based, pH neutral and microbial enzymatic.
Each cleaning agent was found to react differently to flooring and a floor finish. According to CNA’s study, the varying products used to clean a floor often are the direct cause of a slip or fall.
“There’s no exact percent, but I would estimate that on average 20 to 25 percent of the businesses we tested weren’t using the proper cleaning agent,” said Falkenburg.
While seemingly a small part of the floor maintenance process, choosing the right cleaner can have a significant impact on overall floor safety. Cleaning products are designed to sustain a floor’s original COF, so when improperly applied, the friction measurement can be changed.
CNA also looked at nine different categories of flooring in its study. The researchers recorded the natural COF levels, each floor type’s level of slipperiness when wet and what they were made of, from laminated to honed stone.
Linoleum, a resilient flooring typically used in hospital and health care settings, for example, was deemed to have a naturally low COF. It’s a surface that tends to have some type of polymer coating and is intended for dry applications only.
“Insurance carriers and brokers educated [in slip resistance testing and floor maintenance protocols] have a better understanding of the risks. This helps start the conversation on what a business needs to prevent liability and workers’ compensation incidents from occurring.” — Steve Hernandez, senior VP, Risk Control, CNA
CNA dug deeper by testing the floors for DCOF — dynamic coefficient of friction — pre- and post-cleaning, noting how certain cleaners interacted with each floor type. Acidic-based cleaners required a thorough rinsing to achieve maximum cleanliness, while microbial enzymatic cleaners required no surface rinsing post-cleaning.
Overall, CNA advised business owners to look at five things when maintaining their flooring: material used, surface type, condition of the floor, cleaners used and whether the material has a finish on it. (Alkaline-based cleaners removed finishes in some cases. A neutral pH-based cleaner would be better for such flooring.)
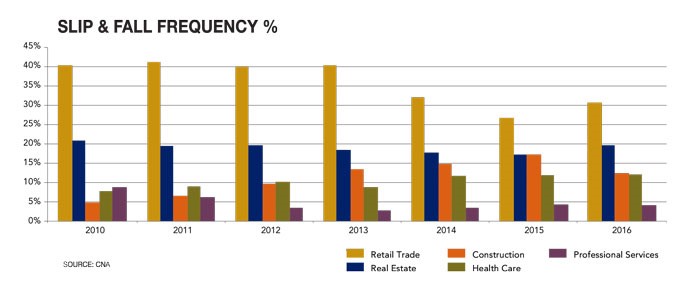
Retail and real estate businesses continue to present the greatest potential for slip and fall accidents. But construction and health care have seen steady increases as well.
Businesses should obtain the designated COF for each of their floor surfaces directly from the manufacturer, the study said.
“Insurance carriers and brokers educated [in slip resistance testing and floor maintenance protocols] have a better understanding of the risks,” said Hernandez. “This helps start the conversation on what a business needs to prevent liability and workers’ compensation incidents from occurring.”
“Risk managers can have conversations with their vendors to discuss floor maintenance procedures, including selection and application of cleaning agents and cleaning equipment utilized. Vendor agreements should incorporate these elements.”
“There’s more risk awareness needed, based on the findings in the study,” added Falkenburg. “Business owners should conduct a needs analysis of their walkway safety management to recognize hidden walkway risks including floor contaminants.”
For instance, she said, they may come across an entrance way with a glare. This glare can lead to poor visibility and increased slips and falls. To prevent such accidents, businesses can add a rug or a plant to the area. “Give the brain something else to look at and observe,” she said.
Slips and falls are a physical peril. “Therefore, it’s a risk we can measure and take actions to reduce or mitigate. With the proper focus on floor testing, we can use trial and error until we have the proper controls in place to yield a passing DCOF value,” said Falkenburg. &











