Sponsored Content by AIG
Proactive Brexit Preparations Promise Seamless Service for Insureds

Since the day the term was coined, “Brexit” has been synonymous with complexity and uncertainty.
UK businesses don’t fully know what to expect once the break becomes final, but U.S. multinationals may feel even more in the dark. Unlike in the UK, media coverage of developments is sporadic in the U.S.
After UK voters decided to exit the European Union in a referendum held on June 23, 2016, the UK government triggered Article 50 on March 29, 2017 — the only law governing the process of separation. Article 50, signed at the Treaty of Lisbon in 2007, gives any member of the EU the right to leave the Union and allows the seceding nation two years to negotiate an exit deal.
With one year down and one still to go until the Brexit becomes final, nothing is yet set in stone.
“Two years is simply not enough time to unravel the decades spent working in a single market,” said Lulu O’Leary, Major Initiatives Office Director, AIG. “The decision was made with very little legislation in place to set a foundation for how this process would go. There was no real framework for what would change and how.”
Over the past year, leaders, legislators and regulators have hashed out initial negotiations around past ties and commitments regarding trade and immigration, but much work remains.
Acknowledging this, negotiators will spend this year building a provisional transition agreement to be ratified in Q4 2018 or Q1 2019 and become legally binding when the break is official in March, 2019. This proposed transition agreement would essentially establish a ‘standstill,’ during which time whatever is in place — immigration rules, financial regulations, trade arrangements — would remain that way while discussion around the details continues.
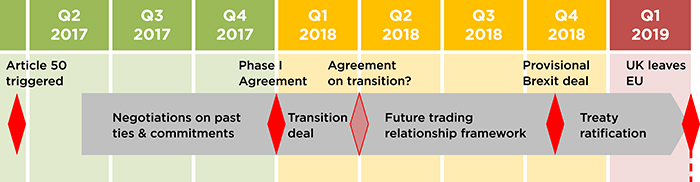 The timeline above demonstrates how the process will move forward over the next year.
The timeline above demonstrates how the process will move forward over the next year.
“The Article 50 withdrawal agreement will include transitional arrangements along with a framework for a future trading relationship and key terms for unwinding the UK’s past ties and commitments,” O’Leary said. “But as the EU’s chief negotiator Michel Barnier often repeats, nothing is agreed until everything is agreed.”
While the provisional agreement extends the timeframe to finalize negotiations, it’s no reason for companies to rest on their laurels or stall contingency planning. Many regulatory questions still await an answer.
The Impact of Reinstated Regulatory Barriers

Lulu O’Leary, Major Initiatives Office Director
While any legal decisions are far from final, there are a few regulatory changes set to complicate the way multinational companies do business.
Loss of Freedom of Establishment and Freedom of Services may require institutions to create entirely new procedures to transact international business legally. Freedom of Establishment grants insurers the right to establish a network of branches or subsidiaries in other EU member states outside the UK and underwrite local risks from those offices. Freedom of Services also gives financial institutions the right to sell services across the EU without regulatory barriers. In the financial services sector, these ‘passporting rights’ are a key building block of what creates the single open market within the European Economic Area (the “EEA”).
Without these rights, UK-based insurers will typically no longer be able to write coverage for risks located in EU member states. It should remain possible for a UK insurer to have branch in an EEA country to write risks located there, but that branch would have to be fully capitalized and prudentially regulated by the local regulator. The ability to conduct cross-border business will depend on the relationships established between the UK’s Prudential Regulation Authority and Financial Conduct Authority and regulators throughout the EU.
Although the UK government has shown some willingness to be flexible around enabling EU insurers who have written policies in the UK to continue to administer those policies on a cross-border basis following the expiry of transitional arrangements, the European Insurance and Occupational Pensions Authority (“EIOPA”) has so far remained rigid in its public statements around UK insurers’ ability to do likewise into the EEA. In a worst case, this could impact the ability to pay claims.

Nuno Antunes, Head of Multinational – EMEA
Multinational companies who rely on the London market to insure their entities and operations overseas throughout Europe may have to re-structure their programs to comply with revised regulations.
“Right now, a U.S. company can come to London and cover all of their risks throughout the UK and the EU with a single policy. Post-Brexit, that likely won’t be possible,” said Nuno Antunes, Senior Vice President, EMEA Head of Multinational and Captive Fronting, AIG. “They’ll have to place separate policies for UK and EU entities, written by insurers with proper jurisdictional authorization.”
“The general view is that a UK-based company will not be able to freely set up branches in Europe, or write business for the European market,” O’Leary said. “If UK-based carriers don’t restructure properly, they may not legally be allowed to pay claims on losses incurred in Europe once the separation is complete.”
Best-in-class carriers aren’t waiting to see how the negotiations play out. Even before the vote was decided, AIG began assembling a structure that would be resilient through the transition period and beyond, without disrupting customer experience.
A Resilient Restructuring

“Even before the referendum, we asked ourselves ‘How do we set up our infrastructure so we can continue to operate across borders in an environment where the existing legal structures may no longer be available?’” Antunes said.
To continue writing international coverage without freedom of establishment or freedom of services to fall back on, AIG recognized the need to establish a separate entity in Europe. Working with regulators in both regions, the company created two new firms — one based in the UK, and one based in Luxembourg.
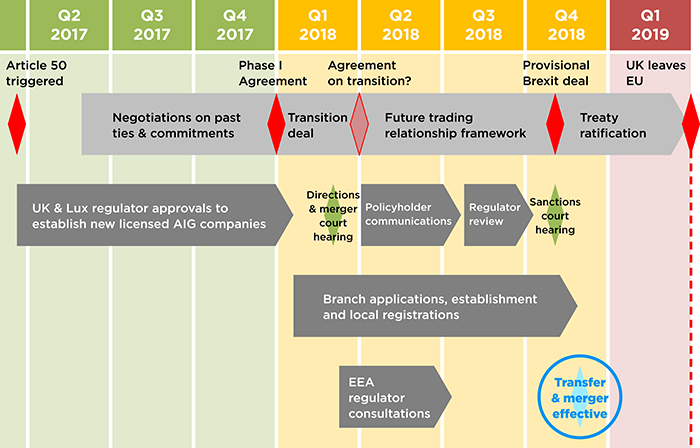
The Luxembourg company, AIG Europe SA, includes 19 branches across Europe and will continue to underwrite European risks, while AIG UK will cover UK-based risks. This new structure is expected to be operational December 1, 2018.
“We will transfer our back-book of business – anything written or renewing by December 1 – into these new entities to ensure business continuity and contract certainty,” O’Leary said. “In other words, we aren’t relying on grandfathering rules. We are prepared for the hardest of Brexit scenarios.”
UK and Luxembourg regulators have already approved licenses for the two new companies. In early March, the High Court of England and Wales approved AIG’s plan for communicating the changes to its policyholders and other interested parties. The year ahead will involve working with regulators to create and license branches throughout Europe and preparing to operate from the two new companies.
“We’ve created a solution that’s seamless for clients. They can continue to work with us as they always have,” Antunes said. “We will have the flexibility to interact with clients how they want to interact with us and do what’s best for them in terms of the structure of their programs, in a fully compliant and legal way.”
Multinational corporations operating in the UK and Europe will have a laundry list of factors to consider as Brexit approaches, but their insurance coverage doesn’t have to be one of them.
“We haven’t shied away from the complexity and we have taken a leadership position in the industry in tackling Brexit head on,” O’Leary said. “Regardless of any political upheavals, AIG will be ready to serve our customers.”
To learn more, visit https://www.aig.com/brexit.
This article was produced by the R&I Brand Studio, a unit of the advertising department of Risk & Insurance, in collaboration with AIG. The editorial staff of Risk & Insurance had no role in its preparation.









