2016 Most Dangerous Emerging Risks
The Fractured Future
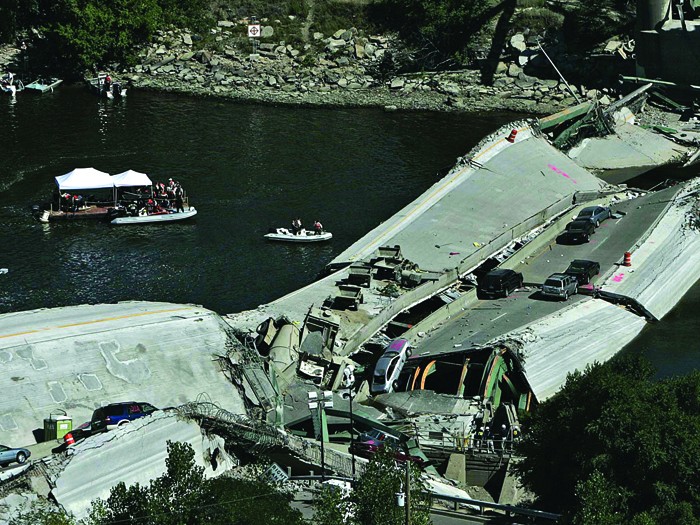
Clipped genetic codes and broken bridges; fragmented communication; electricity networks so vulnerable to interference it’s a wonder we still have the lights on.
As we developed our list of Most Dangerous Emerging Risks for 2016, images of fissures and fractures surfaced again and again.
In this issue, we examine four emerging, dangerous risks. We define a Most Dangerous Emerging Risk as a risk with the potential to cause widespread losses, but for which insurance coverage may be in a nascent stage of development.
On one front, we look at our tendency to self-curate media sources to the degree that informed, official statements get overlooked. Look no further than the phenomenon of parents bypassing vaccinations for their children, fed by an erroneous correlation between inoculation and autism.
We all fear terror attacks. We all worry about cyber hacks. Combine the two and you get the possibility that a cyber attack on our grid could cascade into widespread business interruption and public
disarray for months on end.
On another front, we pronounce a day of reckoning due to a shortfall in both the political will and the resources to maintain our country’s infrastructure. The thousands of children exposed to lead in Flint’s drinking water and the 90,000 metric tons of methane released from a gas well in Porter Ranch, Calif., provide foreboding data points.
Another emerging concern is our new ability to cut and paste DNA strands, and the potential that gene-edited products could hit store shelves before the risk is adequately measured.
We all fear terror attacks. We all worry about cyber hacks.
Combine the two and you get a dangerous emerging risk, the possibility that a cyber attack on our grid could cascade into widespread business interruption and public disarray for months on end.
We spoke to a number of industry experts to create the 2016 Most Dangerous Emerging Risks list; carriers, brokers and vendors were consulted.
The spirit of this exercise is to foster a dialogue in the risk management community about what insurance products might be useful and what risk mitigation strategies companies should be considering right now.
As the years unfold, we see companies and public entities reacting to emerging risks and taking steps to mitigate them. What follows is a list of some risks we’ve written about in the past and measures being taken to mitigate those risks. &
Mitigating Dangerous Emerging Risks
Since 2011, Risk & Insurance® identified and reported on the Most Dangerous Emerging Risks. Here is a look at how some of those risks are now being addressed.
2011: Social Media Threats
 Employee and customer posts to Facebook, Twitter and other social media harm corporate reputations. Companies invested in analytical and monitoring tools and created crisis management plans to respond to critical or brand-damaging posts. Some companies fought back using legal means. One car dealership in Massachusetts obtained a $700,000 attachment on the real estate holdings and bank accounts of individuals who posted defamatory statements about the company online.
Employee and customer posts to Facebook, Twitter and other social media harm corporate reputations. Companies invested in analytical and monitoring tools and created crisis management plans to respond to critical or brand-damaging posts. Some companies fought back using legal means. One car dealership in Massachusetts obtained a $700,000 attachment on the real estate holdings and bank accounts of individuals who posted defamatory statements about the company online.
2011: Rising Sea Levels
 Climate change is resulting in rising sea levels and increased inland flood risk. Local governments are responding to climate change by analyzing specific threats and taking action. In Boston and New York, wastewater treatment plants will be constructed nearly two feet higher than the plants they are replacing. In the San Francisco Bay area, the region is considering a limit on development near the water and the construction of levees and sea walls to keep the sea from encroaching.
Climate change is resulting in rising sea levels and increased inland flood risk. Local governments are responding to climate change by analyzing specific threats and taking action. In Boston and New York, wastewater treatment plants will be constructed nearly two feet higher than the plants they are replacing. In the San Francisco Bay area, the region is considering a limit on development near the water and the construction of levees and sea walls to keep the sea from encroaching.
2012: Typhoons
 The semiconductor industry face supply chain risks because many of its crucial suppliers in the straits of Taiwan are vulnerable to Pacific storms. More companies established relationships with alternative suppliers not located in the same geographic areas or countries. Korea, China and Japan have all become manufacturing locations competing with Taiwan. In addition, some companies are considering reshoring operations to the United States.
The semiconductor industry face supply chain risks because many of its crucial suppliers in the straits of Taiwan are vulnerable to Pacific storms. More companies established relationships with alternative suppliers not located in the same geographic areas or countries. Korea, China and Japan have all become manufacturing locations competing with Taiwan. In addition, some companies are considering reshoring operations to the United States.
2012: Agroterrorism
 We wrote about the potential for terrorists to introduce disease into the U.S. cattle population, decimating ranchers and food suppliers. Food production plants have installed security padlocks and fencing, while milk producers and transporters have security on trucks that will let the company know if the product has been accessed. In 2013, the Food and Drug Administration upgraded its Food Defense Mitigation Strategies Database to provide food processors and distributors with a tool to protect food against intentional contamination. The tool provides a range of preventive measures companies can take to better protect their facilities, personnel and products.
We wrote about the potential for terrorists to introduce disease into the U.S. cattle population, decimating ranchers and food suppliers. Food production plants have installed security padlocks and fencing, while milk producers and transporters have security on trucks that will let the company know if the product has been accessed. In 2013, the Food and Drug Administration upgraded its Food Defense Mitigation Strategies Database to provide food processors and distributors with a tool to protect food against intentional contamination. The tool provides a range of preventive measures companies can take to better protect their facilities, personnel and products.
2012: The Pharma-Water Syndrome
 Hormonal and developmental imbalances in juveniles are a sign that drinking water is adulterated with discarded medications. Some municipalities are testing fish and water samples to determine the amount of chemicals in the water. Many local governments created drug take-back programs that allow residents to drop off unused medications, and the Environmental Protection Agency issued guidelines to discourage hospitals and nursing homes from flushing unused drugs down drains or toilets.
Hormonal and developmental imbalances in juveniles are a sign that drinking water is adulterated with discarded medications. Some municipalities are testing fish and water samples to determine the amount of chemicals in the water. Many local governments created drug take-back programs that allow residents to drop off unused medications, and the Environmental Protection Agency issued guidelines to discourage hospitals and nursing homes from flushing unused drugs down drains or toilets.
2013/2015: Concussions
 In 2013, the potential liability resulting from concussions spread from the National Football League to all professional contact sports. In 2015, the exposure reaches athletes of all ages, from college down to community sports leagues. Ivy League coaches are eliminating tackling at practices to prevent concussions while some high school districts have eliminated football from their sports schedules.
In 2013, the potential liability resulting from concussions spread from the National Football League to all professional contact sports. In 2015, the exposure reaches athletes of all ages, from college down to community sports leagues. Ivy League coaches are eliminating tackling at practices to prevent concussions while some high school districts have eliminated football from their sports schedules.
Forty-nine states and the District of Columbia enacted strong youth sports concussion safety laws.
2014: Drone Hacking
 Devastation could occur if terrorists hacked drones and aimed them at airplanes or other targets. Police in the Netherlands joined forces with Guard From Above to use trained eagles to snatch rogue drones in mid-air. European aerospace conglomerate Airbus uses a combination of radars, infrared cameras and direction finders to identify possible rogue drones. A UK start-up called Open Works Engineering launched an anti-drone net bazooka that can capture a rogue drone in a net and deliver it intact via a combination of a compressed-gas-powered smart launcher and an intelligent programmable projectile.
Devastation could occur if terrorists hacked drones and aimed them at airplanes or other targets. Police in the Netherlands joined forces with Guard From Above to use trained eagles to snatch rogue drones in mid-air. European aerospace conglomerate Airbus uses a combination of radars, infrared cameras and direction finders to identify possible rogue drones. A UK start-up called Open Works Engineering launched an anti-drone net bazooka that can capture a rogue drone in a net and deliver it intact via a combination of a compressed-gas-powered smart launcher and an intelligent programmable projectile.
2016’s Most Dangerous Emerging Risks
 Crumbling Infrastructure: Day of Reckoning Our health and economy are increasingly exposed to a long-documented but ignored risk.
Crumbling Infrastructure: Day of Reckoning Our health and economy are increasingly exposed to a long-documented but ignored risk.
 Cyber Grid Attack: A Cascading Impact The aggregated impact of a cyber attack on the U.S. power grid causes huge economic losses and upheaval.
Cyber Grid Attack: A Cascading Impact The aggregated impact of a cyber attack on the U.S. power grid causes huge economic losses and upheaval.
 Fragmented Voice of Authority: Experts Can Speak but Who’s Listening? Myopic decision-making fostered by self-selected information sources results in societal and economic harm.
Fragmented Voice of Authority: Experts Can Speak but Who’s Listening? Myopic decision-making fostered by self-selected information sources results in societal and economic harm.
 Gene Editing: The Devil’s in the DNA Biotechnology breakthroughs can provide great benefits to society, but the risks can’t be ignored.
Gene Editing: The Devil’s in the DNA Biotechnology breakthroughs can provide great benefits to society, but the risks can’t be ignored.










