The Profession
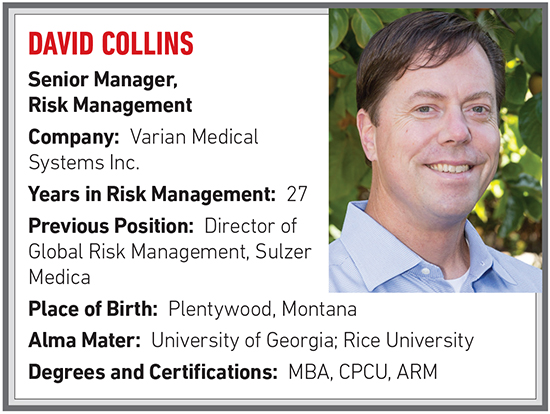
David Collins
R&I: What was your first job?
When I was 15 years old I had a summer job working for the city of Plentywood, mowing grass in the parks and ballfields, emptying garbage cans, hauling waste to the dump, painting crosswalk lines. A great job for a teenager but I thought getting a college degree and working in an air-conditioned office would be a good plan long term.
R&I: How did you come to work in risk management?
I was enrolled in the University of Montana as a general business student, and I wanted to declare a more specialized major during my sophomore year. I was working for my dad at his insurance agency over the summer, and taking new agent training coursework on property/casualty risks in my spare time, so I had an appreciation for insurance. My dad suggested I research risk management for a career, and I transferred sight unseen to the University of Georgia to enroll in their risk management program. I did an internship as a senior with the risk management department at Sulzer Medica, and they offered me a full time job.
R&I: What could the risk management community be doing a better job of?
We need to do a better job of saying yes. We tend to want to say no to many risks, but there are upside benefits to some risks. If we initiate a collaborative exercise with the risk owners — people who may have unique knowledge about that particular risk — and include a cross section of people from other corporate functions, you can do an effective job of taking the risk apart to analyze it, figure out a way to manage that exposure, and then reap the upside benefits while reducing the downside exposure. That can be done with new products and new service offerings, when there isn’t coverage available for a risk. It’s asking, is there anything we can do to reduce the risk without transferring it?
R&I: What emerging commercial risk most concerns you?
Cyber liability. There’s so much at stake and the bad guys are getting more resourceful every day. At Varian, our first approach is to try to make our systems and products more resilient, so we’re trying to direct resources to preventing it from happening in the first place. It’s a huge reputation risk if one of our products or systems were compromised, so we want to avoid that at all costs.
We need to do a better job of saying yes. We tend to want to say no to many risks, but there are upside benefits to some risks.
R&I: What insurance carrier do you have the highest opinion of?
I’ve worked with a number of great ones over the years. We’ve enjoyed a great property insurance relationship with Zurich. Their loss control services are very valuable to us. On the umbrella liability side, it’s been great partnering with companies like Swiss Re and Berkley Life Sciences because they’ve put in the time and effort to understand our unique risk exposures.
R&I: How much business do you do direct versus going through a broker?
One hundred percent through a broker. I view our broker as an extension of our risk management team. We benefit from each team member’s respective area of expertise and experience.
R&I: Is the contingent commission controversy overblown?
I think so. The brokers were kind of villainized by Spitzer. I think it’s fair for brokers and insurers to make a reasonable profit, and if a portion of their profit came from contingent commissions, I’m fine with that. But I do appreciate the transparency and disclosure that came out as a result of the fiasco.
R&I: Are you optimistic about the US economy or pessimistic and why?
While we might be doing fine here in the U.S. from an economic perspective, the Middle East is a mess, and we’re living with nuclear threat from North Korea. But hope springs eternal, so I’m cautiously optimistic. I’m hoping saner minds prevail and our leaders throughout the world work together to make things better.
R&I: Who is your mentor and why?
My Dad got me started down the insurance and risk path. I’ve also been fortunate to work for or with a number of University of Georgia alumni who’ve been mentors for me. I’ve worked side by side with Karen Epermanis, Michael Rousseau, and Elisha Finney. And I’ve worked with Daniel Dean in his capacity as a broker.
R&I: What have you accomplished that you are proudest of?
Raising my kids. I have a 15-year-old and 12-year-old, and they’re making mom and dad proud of the people they’re turning into.
On a professional level, a recent one would be the creation and implementation of our global travel risk program, which was a combined effort between security, travel and risk functions.
We have a huge team of service personnel around the world, traveling to customer sites to do maintenance and repair. We needed a way to track, monitor and communicate with them. We may need to make security arrangements or vet their lodging in some circumstances.
R&I: What do your friends and family think you do?
My 12-year-old son thought my job responsibilities could be summed up as a “professional worrier.” And that’s not too far off.
R&I: What about this work do you find the most fulfilling or rewarding?
Varian’s mission is to focus energy on saving lives. Proper administration of the risk function puts the company in a better position to financially support research that improves products and capabilities, helps to educate health care providers and support cancer care in general. It means more lives saved from a terrible disease. I’m proud to contribute toward that.
When you meet someone whose cancer has been successfully treated with one of our products, it’s a powerful reward.